Correy Lim
Security Operations Manager
Published June 28, 2023
Updated May 18, 2026
5 min
Ultimate Guide to Digital Signatures
Correy Lim
Security Operations Manager
Summary
The blog explores the shift from traditional ink-on-paper signatures to PDF Digital Signatures. It outlines the limitations of basic e-signatures and intricacies of creating and verifying digital signatures using Public-key Cryptography. The guide section distinguishes between Advanced and Qualified Electronic Signatures, emphasizing their legal recognition; and concludes with how Apryse WebViewer SDK and Server SDK can be used for implementing secure digital signatures.
Introduction
As the world rapidly moves towards a digital future, one common aspect of our day-to-day lives involves applying signatures to legally binding documents, such as agreements or contracts. While this has traditionally been done with ink-on-paper, there are potential drawbacks to this approach, especially as it pertains to legally binding documents.
First and foremost, how does one verify that a contract has not been altered since the time of signing? Parties have come to an agreement based on what was written in the contract; however, there is no guarantee whether the contract was potentially tampered with after signing, and there is no way to irrefutably prove that the contract had not changed since the time of signing.
Furthermore, in an ink-on-paper scenario, how can one be sure the signature irrefutably belongs to the person the signature claims to be?
PDF Digital Signatures provide a much more reliable means of producing a verifiable document after it has been signed.
Create, annotate, and digitally sign PDFs in your browser with Apryse WebViewer. Start your document workflow now
What Is an E-signature?
An e-signature, sometimes known as a Simple Electronic Signature, is a digital representation of a signature, typically without any verifiable electronic information associated with the signature. This is closely analogous to an ink-on-paper signature because, with e-signatures, PDF software cannot guarantee that the document has not been modified since the time of signing with a simple e-signature, given that all it represents is a digital recreation of ink-on-paper signatures.
If the nature of an agreement or contract is a potentially high risk to any of the parties involved, then guaranteeing the integrity of the agreement after the document has been signed would be of high value. This is where Digital Signatures can overcome the shortcomings of traditional ink-on-paper signatures and e-signatures.
What Is a Digital Signature?
PDF Digital Signatures leverage the concept of Public-key Cryptography to produce a document that can be verifiably untampered. This ensures to multiple parties that they are all looking at the same document that has not had any further modifications made to it, say in an example of a legal contract.
"Overall, it's a really good SDK for a web app to work with PDF and other document formats. I used it for one of my PHP projects it's great at generating PDFs you can append pages along with creating digital signatures". Capterra Review - Information Technology & Services Company
Learn how digital signatures ensure document authenticity in the age of AI.
Creating a PDF with a Digital Signature
To explain the technical details of how Digital Signatures can guarantee an untampered document after signing, the original unsigned PDF document is first put through a Hash Function to generate a Hash, which is a specific string of letters and numbers that are guaranteed to always be the same output so long as the input data (the PDF document) has not changed. Guaranteeing that the generated hash is always the same for a given input is critical to the Digital Signature process.
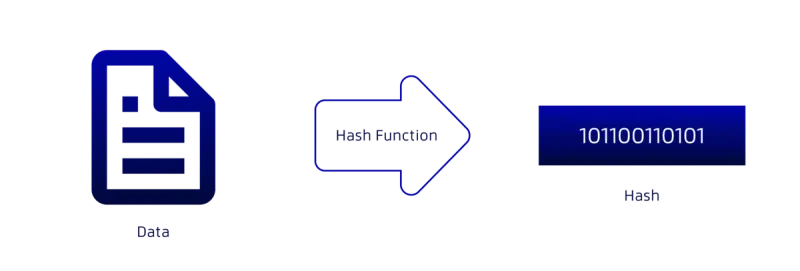
Figure 1. A PDF document being used as input into a Hash Function to produce a Hash output.
The Hash is then encrypted using a Private Key from a Digital Certificate to produce a Digital Signature.
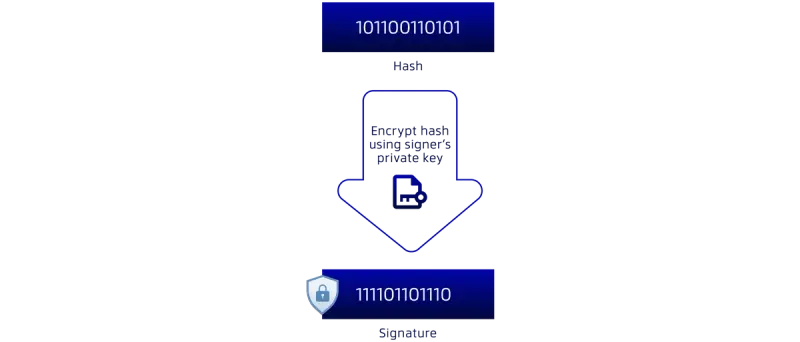
Figure 2. The Hash of the PDF document is then encrypted with the Private Key to produce a Signed Hash.
This Digital Signature is then packaged alongside a Digital Certificate containing the signer’s Public Key into a PDF document.
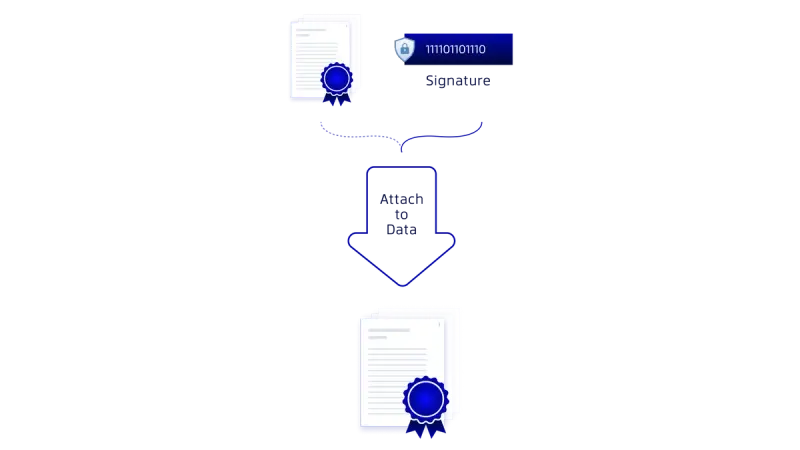
Figure 3. The Public Key Certificate pair of the Private Key used to produce the Signed Hash of the PDF document, and the Signed Hash itself, is packaged into the PDF, producing a PDF with a Digital Signature.
This produces a PDF document with a Digital Signature inside of it.
You may be wondering how this translates into a guaranteed Verifiable document. We'll cover PDF Digital Signature Verification in the following section.
Verifying a PDF with a Digital Signature
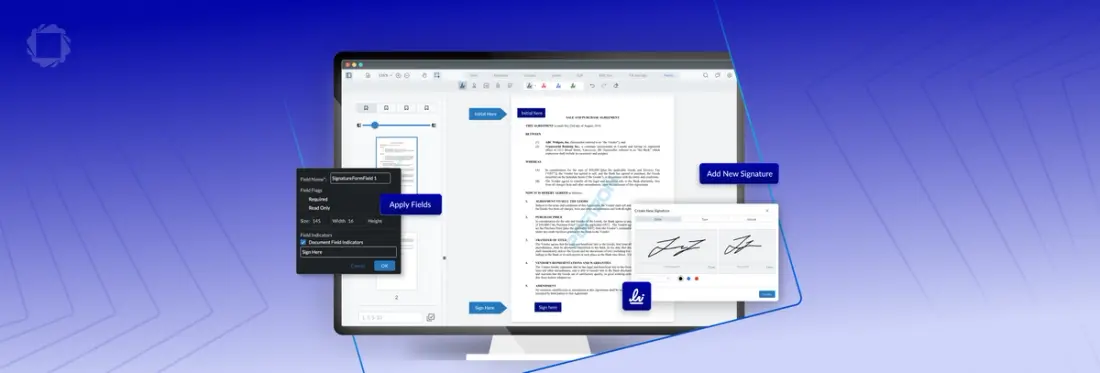
PDF software that can perform PDF Digital Signature Verification, such as Apryse’s WebViewer SDK and Server SDK products, performs two separate steps to verify a Digital Signature.
The first step involves performing a similar operation that was demonstrated in Figure 1. The software verifying the Digital Signature first needs to extract the original document from the Digitally Signed Document.

Figure 4. The original PDF document is extracted from the Digitally Signed Document.
Like the operation performed in Figure 1, the software then processes the original PDF data through the same Hash Function again.
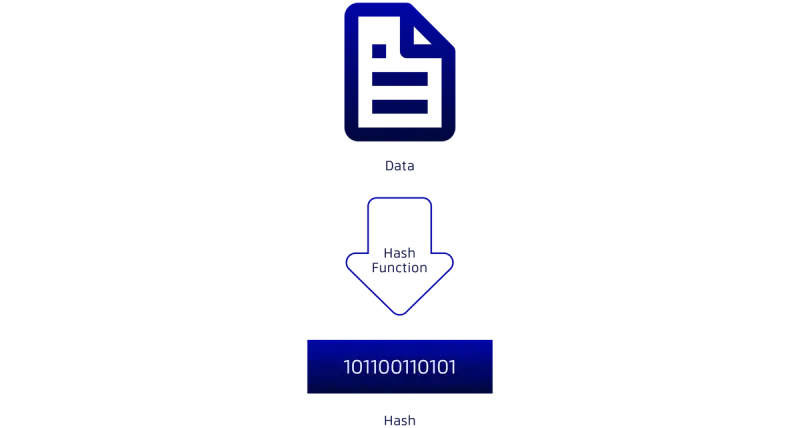
Figure 5. The original PDF document is processed through a Hash Function to produce a Hash output.
Recall that the Hash output will not change so long as the input (i.e., the original PDF) has not changed.

Figure 6. The Digital Signature is extracted from the Digitally Signed Document.
A separate Hash is computed from the Digital Signature that was created in Figure 3. This is done by decrypting the Digital Signature using the Signer’s Public Key that was attached in the PDF in Figure 3.
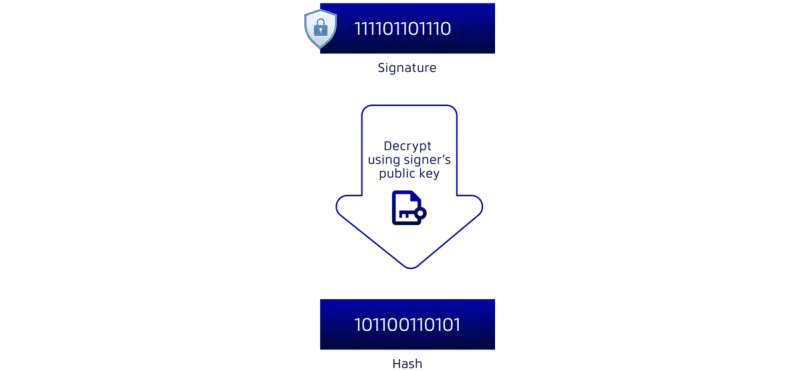
Figure 7. The Digital Signature is decrypted using the Public Key that is asymmetric to the Private Key used to originally generate the Digital Signature.
The two resulting hashes are then compared:
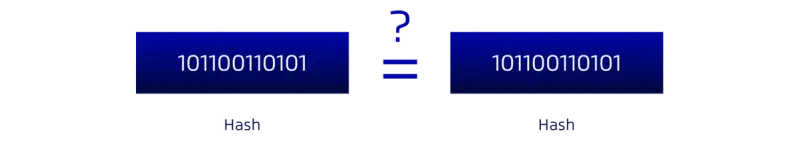
Figure 8. The two separately computed hashes, left representing the hash of the PDF document being processed through the Hash Function once again, right representing the decrypted hash using the Public Key attached in the PDF.
If they match, this guarantees that the document has not been modified since the time the Digital Signature was applied to the PDF document, and the PDF software would reflect this accordingly. If they do not match, then this would indicate that the PDF document is no longer verifiably the same document as the one that Digital Signature was applied to.
Any modifications made to a Digitally Signed PDF will result in the left hash in Figure 8 no longer being equal to the right hash in Figure 8. This means any attempts to change any aspect of a contract or agreement will be flagged by software that can perform Digital Signature Verification, and irrefutably inform readers that the Digitally Signed Document was changed in some way.
Digital Signatures guarantee the integrity of documents, ensuring that a document with a Digital Signature has not been tampered with since the time of signing. This does not require a Certificate Authority.
What are the different types of Digital Signatures?
There are two types of distinct Digital Signatures recognized by government bodies like the European Union (EU):
Advanced Electronic Signature (AES)
1. The signature can be uniquely identified and linked to the signatory.
2. The signatory must have sole control of the electronic signature creation data (typically a private key) that was used to create the signature.
3. The signature must be capable of detecting if its accompanying data was tampered with after the message was signed.
4. If a change in the accompanying data is detected, the signature must be invalidated.
The above walkthrough of the creation and verification of a PDF document with Digital Signatures to guarantee the integrity of the document is a demonstration of creating an Advanced Electronic Signature.To satisfy requirements 1 and 2, free programs like OpenSSL can be used to generate a Public & Private Key pair (in the form of a .pfx file) that can then be used with the Apryse WebViewer SDK or Apryse Server SDK to create a PDF with a Digital Signature.
Add more efficiency to your day-to-day tasks with smart document solutions. Learn how to sign PDFs right from Dropbox.
Qualified Electronic Signature (QES)
A Qualified Electronic Signature (QES) inherits all the properties of an Advanced Electronic Signature, but with a fifth requirement:
5. The Certificate used to create the Electronic Signature must come from a Trusted Service Provider.
A Trust Service Provider is a person or legal entity providing and preserving digital certificates to create and validate electronic signatures and to authenticate their signatories as well as websites in general.
Trust Service Providers may also be Certificate Authorities. Both types of entities can provide Digital Signature Certificates that can be used as part of the Digital Signature creation process.
What Jurisdictions are Digital Signatures Recognized?
Advanced Electronic Signatures and Qualified Electronic Signatures are currently recognized in all European Union countries under EU Regulation No 910/2014, also known as eIDAS. While the United States of America has yet to legally recognize an equivalent of Advanced Electronic Signatures and Qualified Electronic Signatures as has been done in the EU, this could change at any time in the future as the world becomes more reliant on digital technology for executing legally binding contracts.
Learn more about secure and compliant document solutions for the public sector.
"Apryse is a fantastic PDF tool with rich product offerings from annotations to signatures, it has everything covered. Integration of web and SDKs was very easy. Support and documentation are also top-notch." Capterra Review - Health, Wellness & Fitness Company, 51–200 Employees
Next Steps
In this blog post, we covered three different types of signature solutions:
E-signature (Simple Electronic Signature): Functionally equivalent to an ink-on-paper signature, where there is a digital representation of a handwritten signature, with no digital data embedded in the signature to verify the integrity of the document after signing.
Advanced Electronic Signature (AES): Includes Digital Signature data that can be processed by PDF software, such as the Apryse WebViewer SDK or Apryse Server SDK, to verify the integrity of a document to determine if the document has been changed after the Digital Signature was applied.
Qualified Electronic Signature (QES): A more advanced form of the Advanced Electronic Signature, wherein the Digital Signature Certificate used as part of the Digital Signature process originates from a Trusted Service Provider/Certificate Authority.
We hope you have found this guide to PDF Digital Signatures and digital signing technology useful. You can check out our interactive demo for a demonstration of how digital signatures work in the ApryseWebViewer, or see the documentation for the Web SDK to get started quickly. Don’t forget, you can also reach out to us on Discord if you have any issues.